In early 2004 we are dealing with a constant stream of malware sent by email, led by MyDoom and the Bagle and Netsky families.
The spread is fast and affects practically all major Portuguese services, SAPO, Telepac and Netcabo, causing delays and forcing providers to reinforce their filtering systems.
These variants remain active throughout the quarter and often arrive as attachments that appear legitimate, usually accompanied by very short messages encouraging immediate clicking.
Users running Windows XP without updates and with permanent ADSL connections are particularly exposed.
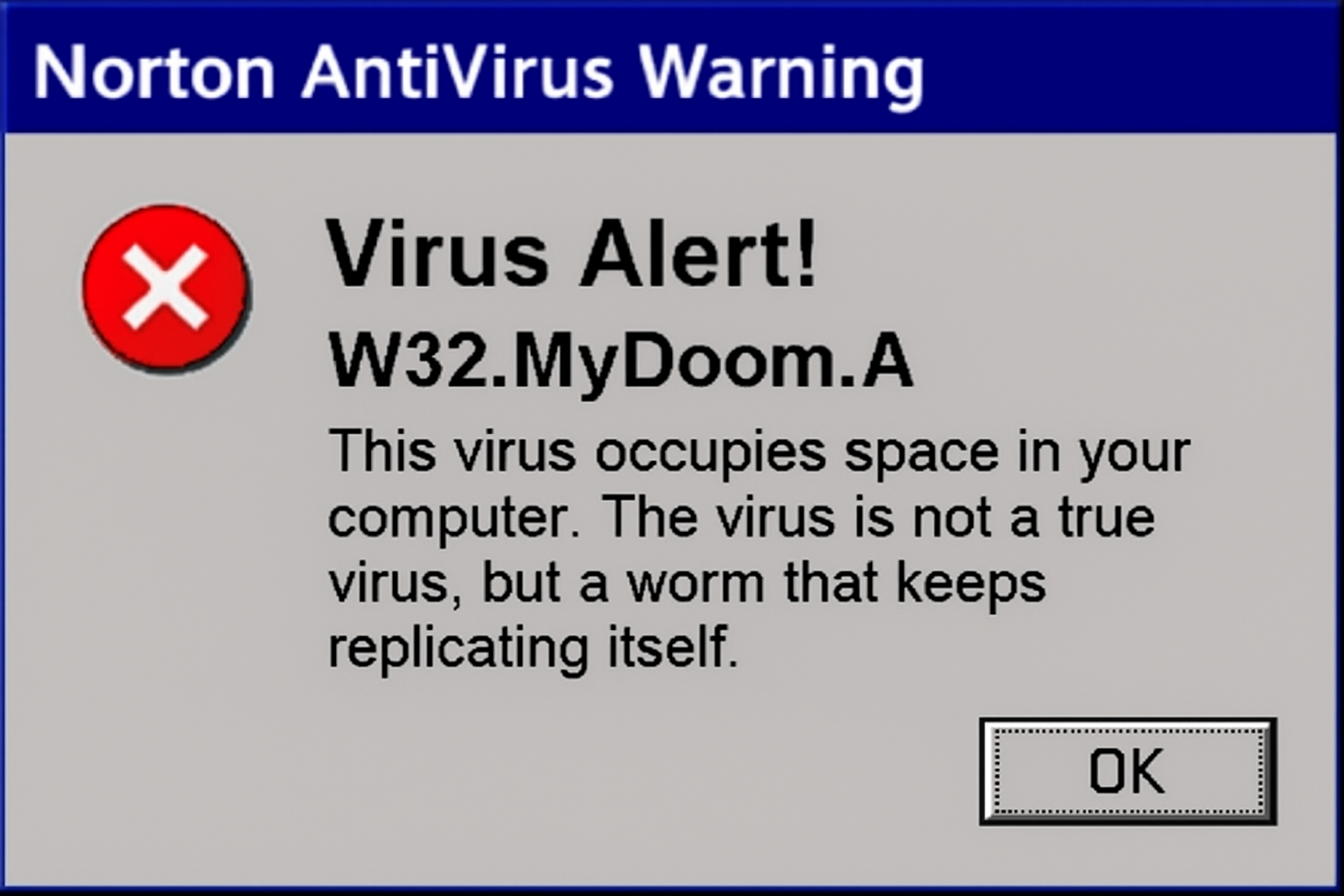
Discovered in January 26, MyDoom.a spread via attached files with the extensions .bat, .cmd, .exe, .pif, .scr or .zip. The worm developes a back door into the system by opening TCP ports 3127 through 3198.
Bagle and Netsky also share an interesting characteristic: each attempts to remove the other from the system, creating additional instability on already compromised machines. We are also seeing users with outdated antivirus software that can’t keep up with the speed at which new variants are released.
Outlook and recommendations
It is likely that next quarter will bring new mutations of these worms, possibly with more convincing social-engineering techniques. The main recommendation continues to be regular antivirus updates and skepticism toward unexpected attachments.
For those using older routers, such as the Thomson SpeedTouch 510, it is advisable to verify that the firewall is enabled, as many units shipped with overly permissive default profiles.